Easy Way In? 5 Ransomware Victims Had Their Pulse Secure VPN Credentials Leaked
Victoria Kivilevich, Threat Intelligence AnalystRising ransomware attacks around the world, together with the recent lists of exposed Pulse Secure VPN credentials set the backdrop for KELA’s latest research. While not all ransomware attacks used CVE-2019-11510 (a vulnerability of unpatched Pulse Secure VPN servers) or the previously shared credentials to the compromised corporate networks, it does add another layer to the analysis of possible initial infection vectors used in ransomware incidents. Moreover, the recent exposure of credentials to nearly 50,000 vulnerable Fortinet VPNs raises further concern of possible infection vectors that can be used for ransomware attacks.
Our key findings include:
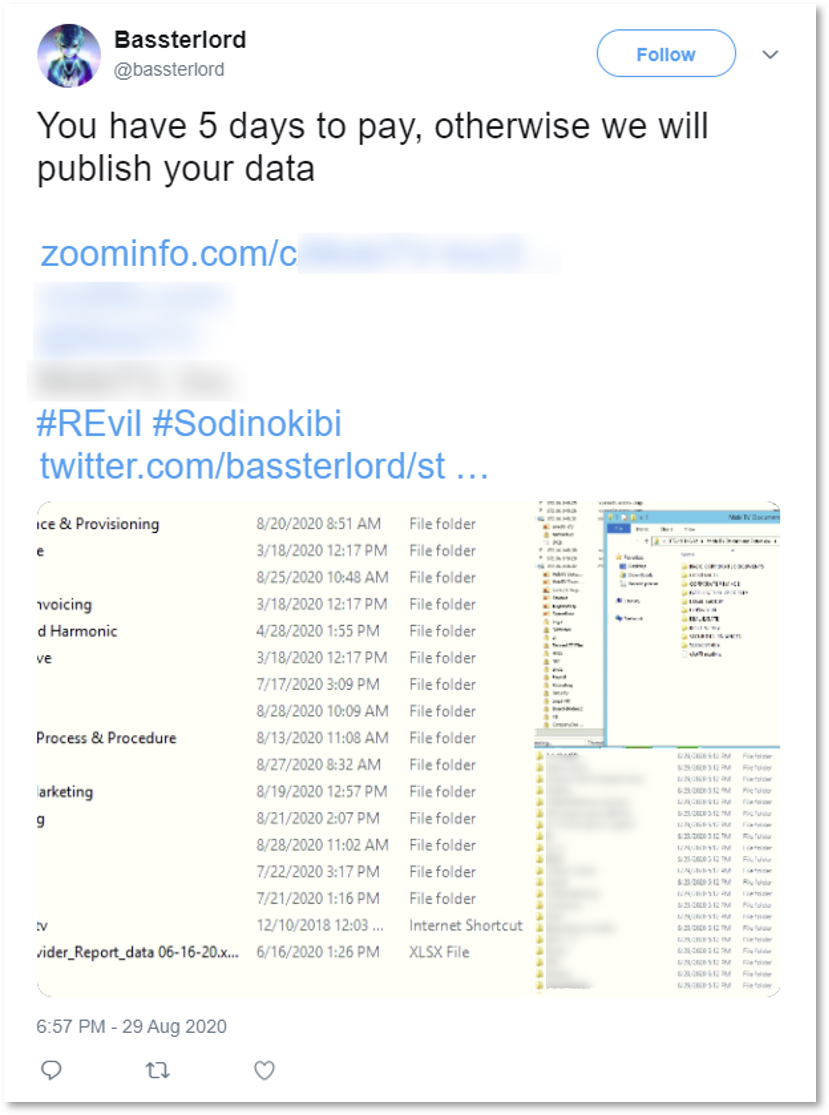
Five victims of ransomware attacks whose credentials to their Pulse Secure VPN servers were exposed as part of two Pulse Secure VPN lists (i.e., directories with folders and files) that were shared by malicious actors in August 2020.
Data of three of the victims were leaked to ransomware gangs’ blogs in an attempt to force them to pay a ransom. Based on KELA’s conversation with threat actors related to the attack, at least one victim (unnamed) paid the ransom.
A threat actor involved in the attack confirmed that they gained initial access to at least one compromised network via the CVE-2019-11510.
Proactive monitoring of darknet threats, such as the Pulse Secure VPN lists, helps enterprise defenders secure their networks and prevent further, more sophisticated attacks, such as ransomware attacks.
