Slacking Off – Slack and the Corporate Attack Surface Landscape – Part 2
Irina Nesterovsky, Chief Research Officer
In our first post referencing Slack and the corporate attack surface, we revealed the 12,000+ credentials to Slack workspaces that were available for sale on various cybercrime underground markets, representing the explicit threat for thousands of organizations. However, at the time, examination of both open-source reporting and cybercrime communities didn’t reveal a lot of attacker-interest in the platform. Though a steady interest may still not be apparent, what is clear is that the number of compromised credentials has grown, and another instance in which Slack credentials have been abused appears once again. Now, a year later from the release of Part 1, we have dived back into those same sources to see what exactly has transformed over the last year, and what the dangers of compromised Slack credentials really may be.
How did Electronic Arts Get Hacked?
Last week, the media was flooded with announcements about the hack on Electronic Arts, which reportedly began with hackers who purchased stolen cookies sold online for just $10. The attack process continued with hackers using those credentials to gain access to a Slack channel used by EA. Once in the Slack channel, those hackers successfully tricked one of EA’s employees to provide a multifactor authentication token, which enabled them to steal multiple source codes for EA games.
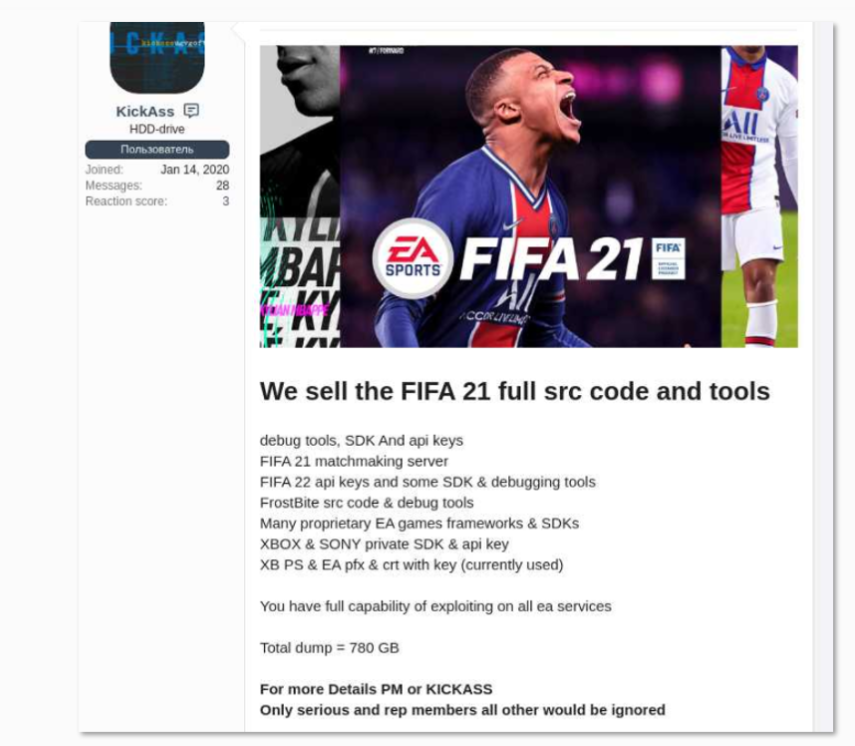
One of the hacker’s posts offering to sell EA data and source code.
This recent incident showcases exactly how cybercriminals continually use the cybercrime underground ecosystem to facilitate breaches – among other types of attacks. In Part 1 of our blog, we discussed another incident in which Slack credentials were acquired and abused by threat actors in a slightly different way, but still proved to be of great use as part of an attack against high-profile Twitter accounts.
There, we were able to understand the simplicity of sourcing sensitive credentials to internal resources, and specifically Slack, from what we call Compromised Accounts – accounts that are found on machines that were compromised by malware and specifically the information-stealer component in those; information from which is sold on dedicated botnet marketplaces such as Genesis. The claimed underlying source of the EA attack now, as well as the Colonial Pipeline investigation, where it was reported that the attack started from abandoned VPN credentials that were later found on the Dark Web – serve a great example of the items that are frequently traded in between cybercriminals. Defenders, however, can aim to stop remediate these types of threat before further damage occurs, by gaining visibility into the inner workings of the underground ecosystem and tracing the same vulnerabilities, exposures and compromises that are being leveraged by threat actors.
Slack Credentials in the Cybercrime Underground Ecosystem
The recent hack on EA demonstrates the booming underground cybercrime ecosystem that is loaded with potential entryways into different organizations’ environments. Looking back into the same sources we research for Part 1 of this blog, we found that there are exposed credentials to over 25,000 workspaces for sale. This means that over 25,000 different companies/organizations had their credentials available for purchase to any buyer, and especially to those who are up to no good.
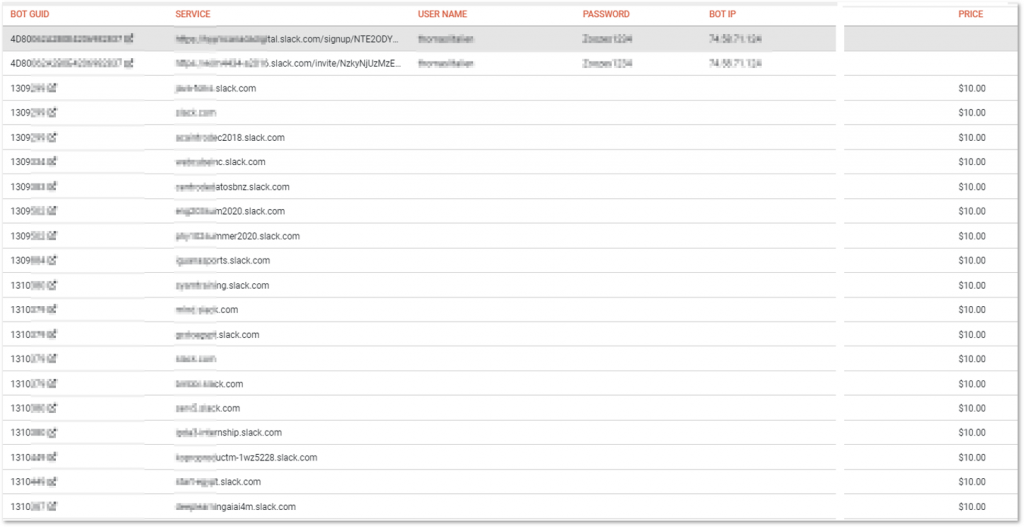
Examples of compromised Slack credentials offered for sale, gathered using KELA’s DarkBeast. Usernames and passwords are available to buyers.
And while the above only refers to the initial potential entry point – we’ve demonstrated in our ongoing research how actors in the cybercrime supply chain, and specifically those we call Initial Access Brokers, strive on those items to facilitate further attacks. We can see them selling access to corporate networks that were no doubt sourced at least in part from such sensitive credentials that are there “for grabs” for a few bucks. Those accesses later end up serving as initial access points in various types of attacks, and specifically ransomware ones, therefore monitoring for such indicators is crucial to help in preventing cyberattacks.